
Driving progress and adoption of identity security for modern enterprises
Make your identity security investment work harder for you
Get In touch
You Came to the Right Place
We help you leverage identity to create new business advantages
If you’ve arrived here, you’re likely in one or more of these scenarios:
Seeking
Seeking
An urgent fix
38%
of our business is fixing competitor failures
Seeking
Seeking
A trusted partner
96%
Customer retention rate
Seeking
Seeking
Assured integration
220+
Identity specialists with certifications
Seeking
Seeking
Scalable operations
58%
of new customers use Managed Operations
Create a Bigger Impact
Capabilities across the identity framework and beyond
Our expertise spans across your enterprise, uncovering value by bringing together disparate knowledge and technology for enterprise-wide program execution.
.svg)
.svg)
.svg)
Workforce Identity
Empower your workforce with zero-trust identity solutions for seamless, secure access—anywhere, on any device, for every user.

Identity Governance
Automate identity governance to simplify compliance, reduce risk, and provide clear, actionable oversight across your enterprise.
.svg)
Customer Identity
Secure and personalize every customer interaction with CIAM solutions that simplify identity management and drive loyalty.

Non-Human Identity
Secure and manage service accounts, bots, and machine identities with automated controls, clear ownership, and robust governance.
.svg)
Privileged Identity
Protect critical assets with automated privileged access management that enforces least privilege and streamlines compliance.
Identity Services
Complete support throughout your identity journey
We offer full lifecycle support with strategic guidance, exceptional delivery, and continued management to drive outcomes in complex environments.
0
1
.svg)
Advisory
Our Advisors work across the technology and vendor landscape, extending expertise to your applications, cloud, and data systems.
0
2
.svg)
Deployment and Integration
With 1,950 projects and counting, our proven innovative approach expands across identity services.
0
3
.svg)
Managed Operations
Deliver greater efficiency, reliability, and business value across your IAM ecosystem with cross-functional identity specialists who optimize performance and drive continuous innovation.



Thank you for restoring my faith in consulting. MajorKey took the time to listen to, understand, and address our challenges. You saved our identity program.
,
Large Private University
Technology Partners
Award-winning partnerships and some of the most certified teams worldwide
Protect and optimize your identity investments with our cross-trained identity specialists and accelerator tools to achieve faster results even better.
Customer Success
Privileged
Zero Trust
Migration
SOX Controls
Automation
Top ranked children's hospital automates new user processing
Top ranked children's hospital automates new user processing
Transformed a leading pediatric healthcare organization’s inefficient SailPoint IdentityIQ user provisioning process—cutting delays, enhancing security, and enabling faster access to critical systems for better care delivery.


2,600
Annual hours saved
Modernizing IGA with a Zero Trust Framework
Modernizing IGA with a Zero Trust Framework
Re-deployed a previously stuck go-live within a Zero Trust framework. The fully deployed solution reduced process complexities; automated IAM, service desk activities, birth-right access for J/M/L; completed certification campaigns and attestations; established continuous controls; and simplified the audit process.



Services
Migration from legacy to cloud identity solution
Migration from legacy to cloud identity solution
Provided workflow enhancements and migrated core business applications from SailPoint IIQ to SailPoint Identity Security Cloud. Enabled stronger integrations, simplified usability, and ongoing maintenance requirements, while simultaneously integrating non-employee visibility and governance.


30 Days
Completed ahead of schedule
Services
Meeting SOX 404 controls and automating SOD
Meeting SOX 404 controls and automating SOD
Fast-tracked new vendor selection process, deployed a modern solution, and integrated with Oracle to meet compliance requirements not able to reach with current solution and automate manual controls.

Accelerate onboarding and offboarding at scale
Accelerate onboarding and offboarding at scale
Deployed and enhanced SailPoint across a multi-year roadmap, meeting massive demand for user onboarding and offboarding, and enabling process improvement with automation


58,000
Users onboarded & offboarded annually

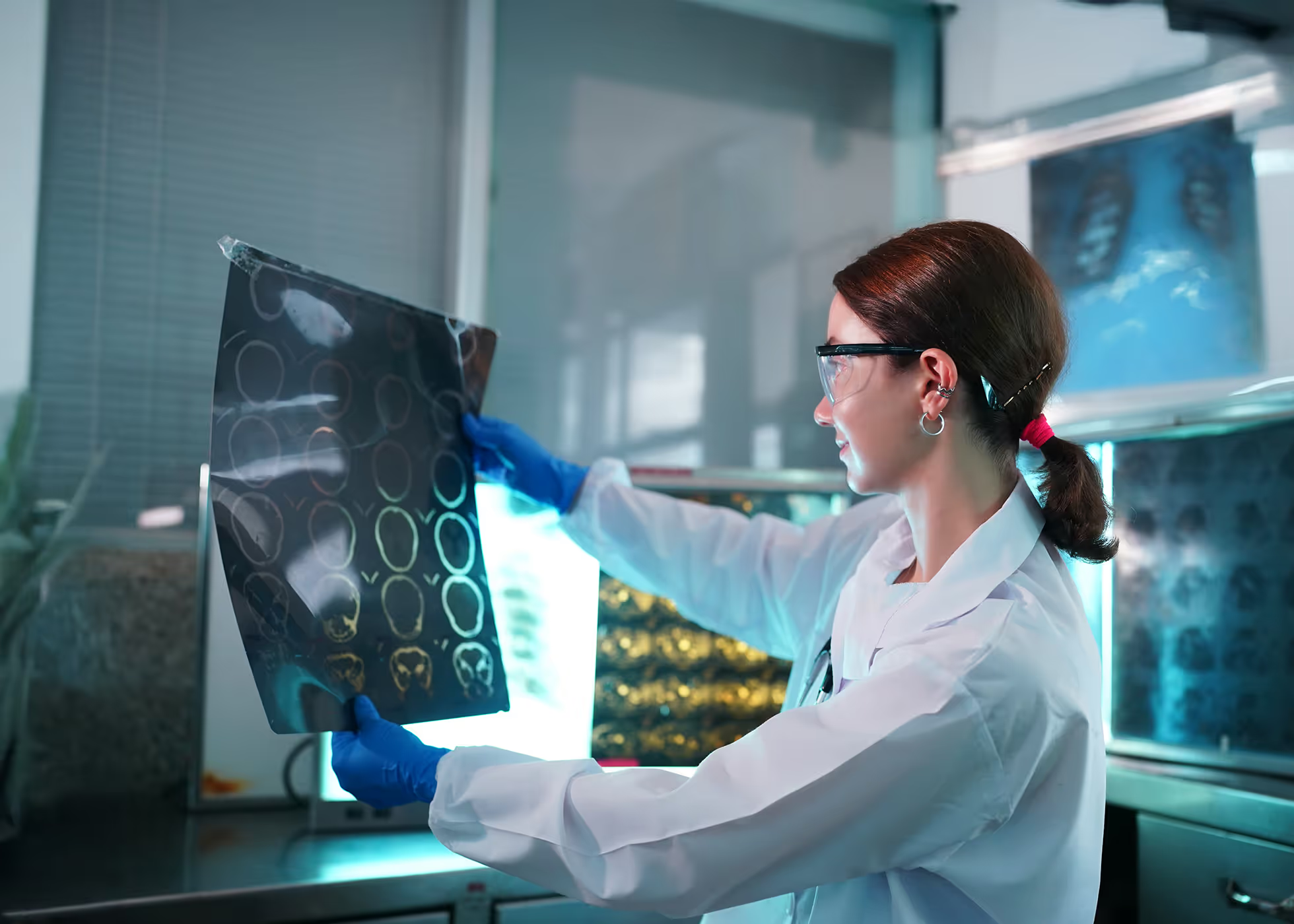
Support Across Industries
Extensive industry knowledge and experience
Our cross-trained team of tenured and certified identity specialists provide unparalleled expertise and execution across private industries and the public sector.
156
Manufacturing sector projects
9 of 15
Top financial institutions served
132
Insurance sector projects
205
Hospital and healthcare sector projects
TRENDING now
Blog


Decentralized Identity Explained: A Practical Q&A for 2026
Explore the key concepts, benefits, challenges, and emerging trends shaping decentralized identity in 2026 and beyond.
March 10, 2026
Learn more
Blog


IGA and Change Management: A Guide to Successful Engagements
When effective change management is integrated with IGA implementations from the start, organizations reduce resistance, increase alignment, and ensure new identity processes take root in a sustainable, scalable way.
March 3, 2026
Learn more
Blog


Outcome‑Driven IAM: Why Identity Programs Win on Results, Not Tools
Why IAM programs fail despite strong tools, and how outcome‑driven IAM delivers measurable risk reduction, audit readiness, and business value.
February 27, 2026
Learn more
Blog


Breaking Down Identity Silos: Why Fragmented Systems Create Risk and Complexity
Learn about the challenges created by identity silos, the trade-offs between consolidation and governance, and how organizations can determine the most effective path forward.
February 20, 2026
Learn more
Blog


Identity Proofing 101: A Practical Guide for Modern Organizations
Discover why identity proofing is a foundational security control for modern organizations.
February 11, 2026
Learn more
Blog


Preparing your Organization for AI-Driven Identity Threats
Learn how AI‑driven identity threats are evolving and why governing AI agents as managed, privileged identities is key to secure, responsible AI adoption.
February 4, 2026
Learn more
Blog


KPIs for App Onboarding: What to Measure and Why It Matters
The most useful KPIs for app onboarding include percent of applications onboarded, time‑to‑onboard, and realized business value or ROI. These metrics give stakeholders clear visibility into progress and help keep the onboarding program accountable and predictable.
January 30, 2026
Learn more
Blog


Have You Solved Your IAM Problem?
Struggling to make sense of your IAM ecosystem? Discover how to overcome tool overload, achieve continuous reliability, and align identity management with business outcomes. Learn practical strategies for visibility, observability, intelligence, and action—plus insights on AI’s impact in modern IAM.
January 8, 2026
Learn more
Blog


Modernizing Identity Governance: Enabling Agility and Compliance Across the Enterprise
Leverage automated onboarding, AI-driven access reviews, and just-in-time least-privilege controls to transform identity governance into a driver of security, compliance, and agility.
December 17, 2025
Learn more
Blog


Mastering Certificate Renewal: How Automation Bridges PKI and Privileged Access
Prepare for 47-day TLS lifespans: automate discovery, ownership, renewal (with new keys), and evidence—integrated with PAM/IAM change control.
December 17, 2025
Learn more
Blog


Accelerating Privileged Access Security: Practical Steps for PAM Automation Success
Learn how to identify quick PAM automations—discovery, rotation, session isolation—then scale JIT/ZSP for audit-ready, resilient privileged access programs.
December 17, 2025
Learn more
Blog


Rethinking Application Onboarding: A Value-Based Approach for Real Business Impact (2025 Navigate Session Recap)
Discover how MajorKey Technologies is transforming identity programs with a value-based approach to application onboarding. Learn why traditional methods fail and explore our KPI-driven strategies to unlock ROI and business speed.
December 5, 2025
Learn more
Blog


Identity Assurance Made Simple: Remote Hiring, Third-Party Access, and Call Center Protection
Discover how IDProof+ prevents identity fraud with biometric checks, global document verification, and Zero Trust access. Protect your workforce and sensitive data today.
November 24, 2025
Learn more
Blog


Securing Modern Identities: How Microsoft Entra ID Governance Transforms Access Management
In part 2 of our Transitioning Beyond MIM Revisited series, we explore Microsoft's rapidly evolving capabilities and their impact on organizations navigating the shift from MIM.
November 20, 2025
Learn more
Blog

Navigating AI Adoption: Identity Security Considerations for Microsoft Copilot
Discover how organizations can securely adopt AI tools like Microsoft Copilot by addressing identity security challenges. Learn about common risks, best practices, and a structured assessment approach to ensure responsible AI integration and compliance.
November 18, 2025
Learn more
Blog

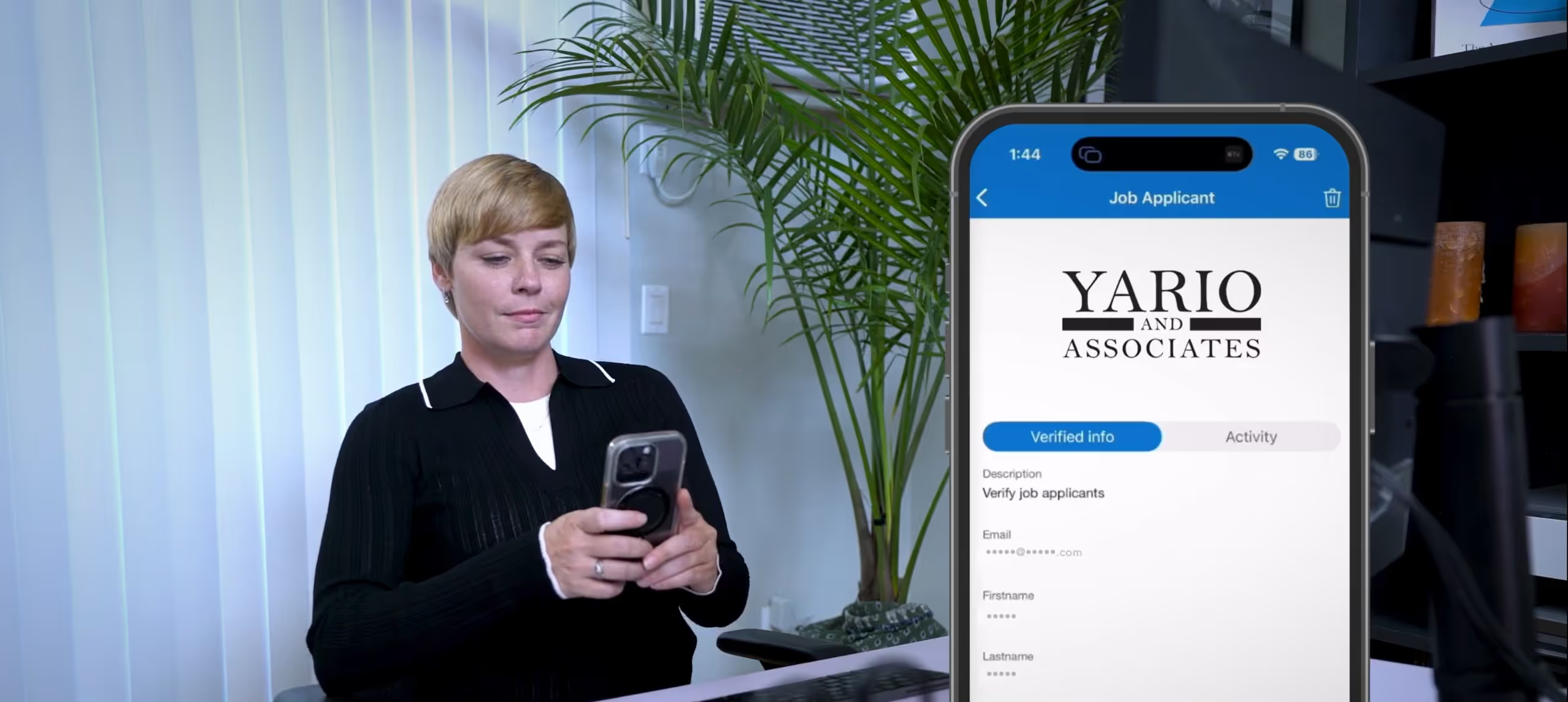
From Deepfakes to Fraudulent Employees: Securing Remote Work
Discover how deepfake fraud and fake employees are reshaping remote work risks—and why identity assurance is critical. IDProof+, integrated with Microsoft Entra Verified ID, helps organizations prevent interview fraud, secure remote hiring, and protect against insider threats.
November 17, 2025
Learn more
Blog


Enhancing Remote Workforce Security: How IDProof+ Is Transforming Identity Verification
Discover how IDProof+'s advanced AI, biometric authentication, and deepfake detection protect organizations from fraud, streamline remote hiring, and ensure GDPR compliance.
November 10, 2025
Learn more
Blog


Transitioning Beyond MIM Revisited, Part 1: The Current MIM Landscape
MIM is now in extended support, but what's the right migration path for your organization? This blog series will examine the options and key considerations to help MIM users to determine their path to the cloud.
November 6, 2025
Learn more
Blog


CyberArk Webinar Series: Transforming Identity Security Through Intelligent Automation
This three-part webinar series brings together leading voices to discuss transforming identity security through intelligent automation.
October 28, 2025
Learn more
Blog

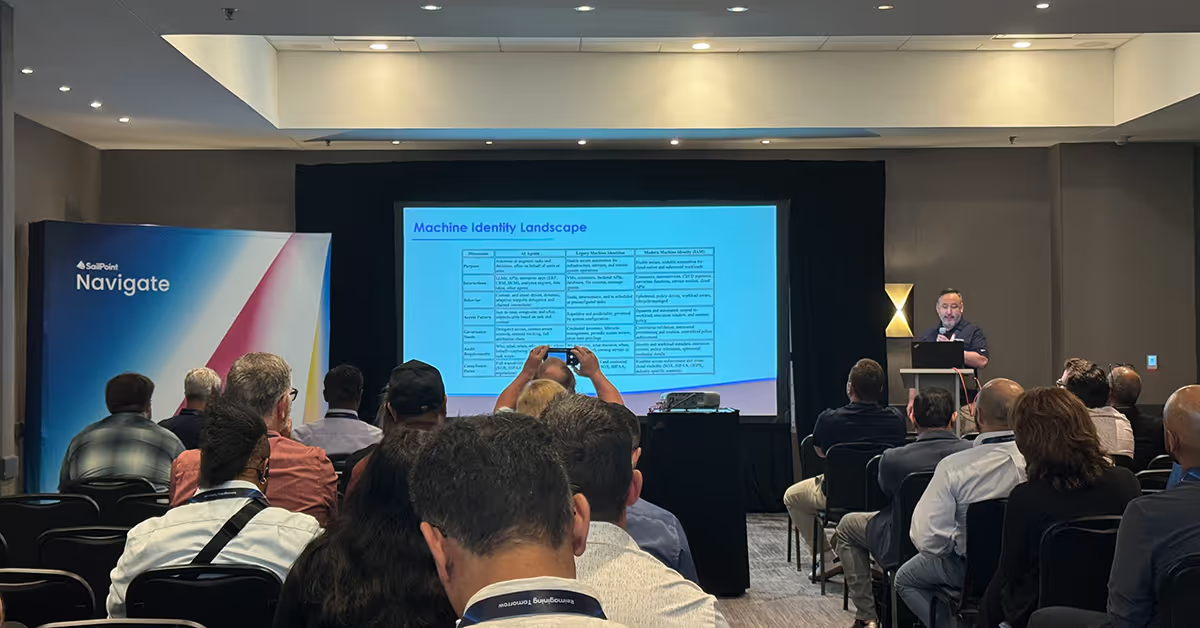
From Shadow to Certainty: Securing Machine Identities with Confidence (2025 Navigate Session Recap)
With machines now outnumbering humans by staggering ratios, unmanaged identities have become a critical, and often overlooked, attack vector that organizations can no longer afford to ignore.
October 16, 2025
Learn more
Blog


6 Highlights from SailPoint Navigate 2025
This year’s SailPoint Navigate conference was a showcase of innovation, technical depth, and community spirit. Here are the six highlights that stood out most from our experience at Navigate 2025.
October 9, 2025
Learn more
Blog


Modernizing Identity Governance with MajorKey’s HorizonID and Microsoft Entra Suite
MajorKey’s HorizonID is a transformative solution that bridges the gap between legacy identity systems and modern cloud-based strategies.
October 1, 2025
Learn more
Blog

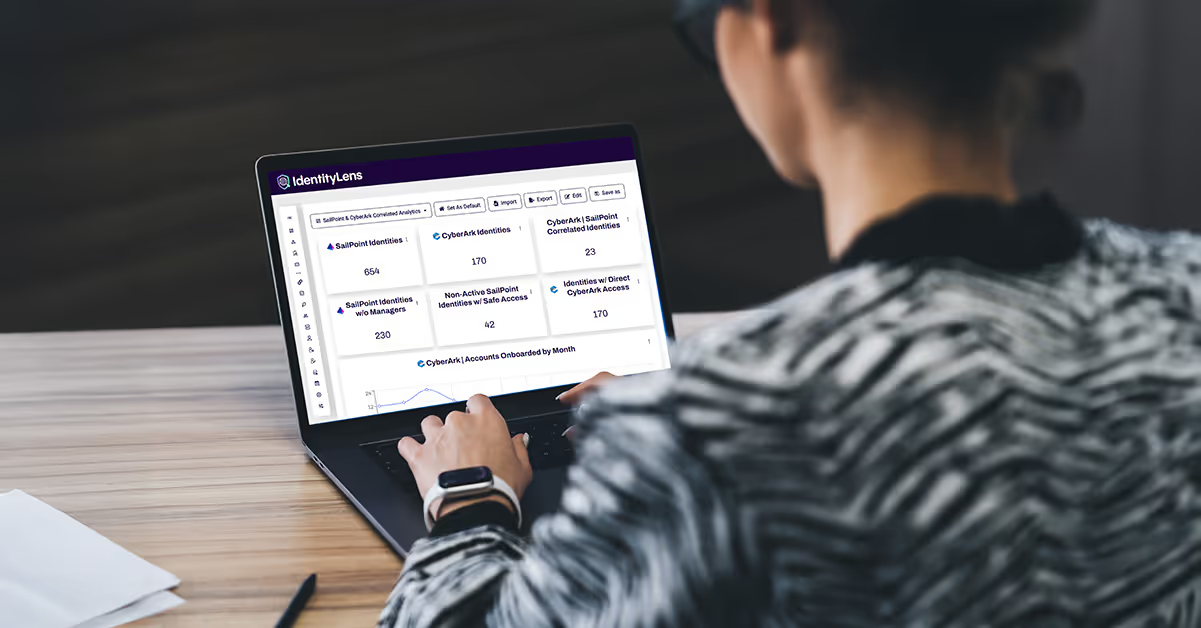
Unlocking Operational Insight: How IdentityLens is Transforming Managed Services
Unlock operational insight with IdentityLens—MajorKey Technologies’ advanced reporting and analytics platform for managed services—empowering organizations with real-time identity data, automated compliance, and actionable dashboards for smarter, safer IT operations.
September 26, 2025
Learn more
Blog


Redefining Efficiency and Reliability: How MajorKey Managed Operations Empowers Identity Programs
Discover how MajorKey’s Managed Operations (MOps) empowers organizations to achieve secure, scalable, and outcome-driven identity management with expert guidance, automation, and 24/7 support. Learn how MOps streamlines operational efficiency, reduces risk, and drives measurable progress for modern identity programs.
September 26, 2025
Learn more
Blog


Digital Trust Reimagined: How Verifiable Credentials and Face Check Help Stop Fraud and Streamline Security
Whether you're securing privileged access, enabling self-service recovery, or modernizing identity, MajorKey’s IDProof+ provides a proven defense against fraud and identity-based threats.
September 8, 2025
Learn more
Blog


Mastering Non-Human Identity Management: Challenges, Strategies, and Executive Alignment
Non-human identities (NHIs) such as service accounts, bots, and API keys operate autonomously across IT environments but often lack proper provisioning, lifecycle management, and oversight, making them a critical security risk. Effective NHI management requires inventory and ownership clarity, strict access controls based on least privilege, automated lifecycle management, continuous monitoring, and executive alignment to reduce breach risks and ensure compliance.
August 22, 2025
Learn more
Blog


Introducing NomadID: Mission-Ready Identity Management for Federal Agencies in DDIL Scenarios
NomadID by MajorKey Technologies is an Identity, Credentialing, and Access Management (ICAM) solution designed for Department of Defense (DOD) and federal agencies operating in Disconnected, Denied, Intermittent, Low-Bandwidth (DDIL) environments. It ensures uninterrupted authentication and single sign-on (SSO) capabilities even during network outages or hostile conditions, combining identity management, security monitoring, and governance locally at the edge to uphold security standards and maintain seamless access in challenging or disconnected scenarios.
August 20, 2025
Learn more
Blog


Selling IAM to the Business: Speak Their Language, Not Yours
Identity and Access Management (IAM) can be sold to business leaders effectively by focusing on business outcomes rather than technical jargon. Emphasizing benefits such as increased employee productivity through streamlined access, faster onboarding with automated provisioning, enhanced audit compliance with automated role management, improved customer loyalty via seamless and secure login experiences, and uninterrupted business operations by ensuring timely access to tools helps connect IAM to revenue growth, customer satisfaction, and operational efficiency.
August 20, 2025
Learn more
Blog


Critical SharePoint On-Premises Zero-Day Vulnerability (CVE-2025-30556) Under Active Attack — Urgent Steps to Protect Your Systems Now
A critical zero-day vulnerability in Microsoft SharePoint Server on-premises, tracked as CVE-2025-53770 and nicknamed "ToolShell," is actively exploited, allowing unauthenticated attackers to execute arbitrary code remotely, potentially compromising entire servers and networks. Microsoft has released emergency patches and mitigation guidance, urging all users to apply updates immediately, enable advanced detection tools like Microsoft Defender, rotate ASP.NET machine keys, and strengthen access governance with Privileged Access Management (PAM) to protect against this severe threat.
July 25, 2025
Learn more
Blog


Why IAM Projects Fail — And How to Flip the Script
Identity and Access Management (IAM) projects fail due to poor planning and stakeholder misalignment. Flip the script with proven success strategies.
July 18, 2025
Learn more
Blog


What is Harbor Pilot? An Intro to SailPoint’s New IAM AI Agent
Harbor Pilot is SailPoint’s AI-driven Identity and Access Management (IAM) assistant. Discover how it streamlines identity decisions with automation.
July 16, 2025
Learn more
Blog


From VPNs to Identity-Driven Access: The Microsoft Entra Global Secure Access Advantage
Microsoft Entra Global Secure Access is a unified Security Service Edge (SSE) platform combining Microsoft Entra Private Access for secure, identity-based access to private applications and Microsoft Entra Internet Access providing cloud-based Secure Web Gateway and threat protection for internet and SaaS access. It enforces Zero Trust principles, centralizes policy management, enables continuous risk assessment, and delivers seamless, agentless user experiences, making it a modern replacement for traditional VPNs.
July 16, 2025
Learn more
Blog


Key Takeaways from Identiverse 2025
Identiverse 2025 highlighted critical trends in identity and access management, including the urgent need for convergence between identity and network access, and the rise of AI agents and non-human identities (NHIs) as major security priorities. The conference emphasized that identity is now a central pillar of organizational strategy, requiring robust governance frameworks to manage AI agents and NHIs, which outnumber human identities by at least 20:1, and underscored the importance of identity resilience, continuous verification, and advanced technologies like behavioral biometrics and decentralized identity to restore trust in digital interactions.
June 18, 2025
Learn more
Blog

The Evolution of IAM: Transforming from Security Necessity to Strategic Value Driver
Identity and Access Management (IAM) has evolved from a security tool to a strategic business enabler. Learn how modern IAM supports digital transformation.
June 2, 2025
Learn more
Blog


5 Common Access Review Pitfalls (and How to Fix Them)
Common access review pitfalls include overwhelming reviewers with too many simultaneous reviews, lack of context about why access is granted, manual processes causing inefficiencies, failure to enforce review outcomes, and involving the wrong stakeholders in the decision-making. Addressing these issues with prioritized, risk-based reviews, actionable insights, automation, enforced remediation, and involving knowledgeable business owners can greatly improve security, compliance, and audit readiness.
May 28, 2025
Learn more
Blog


The Business Case for Lifecycle Workflows in Microsoft Entra ID
Lifecycle workflows boost IAM efficiency and reduce manual errors. Discover how automation drives ROI in identity governance.
May 20, 2025
Learn more
Blog


Microsoft Entra ID Governance: What’s New and Why It Matters
Microsoft Entra ID Governance is an enterprise-grade identity governance solution integrated within the Microsoft Entra platform, designed to automate and streamline identity and access lifecycle management across cloud, on-premises, and hybrid environments. Recent updates include group Source of Authority conversion for cloud-based governance of legacy Active Directory groups, request and lifecycle governance with approval workflows, time-bound access controls, and integration with Microsoft Entra Verified ID for real-time identity verification, enhancing security, compliance, and operational efficiency.
May 14, 2025
Learn more
Blog


Why Identity is the New Perimeter: Rethinking Security in a Cloud-First World
Identity is now the perimeter in cloud-first security models. Learn how Identity and Access Management (IAM) defends against modern threats.
May 5, 2025
Learn more
Blog


What We Learned at CyberArk Impact 2025
CyberArk Impact 2022 revealed trends in privileged access and zero trust. Get expert insights from the IAM frontlines.
April 21, 2025
Learn more
Blog


What is Skydock? A Comprehensive Solution for CyberArk Object Migration
Skydock offers a unified Identity and Access Management (IAM) solution for hybrid environments. Explore its features for secure access and governance.
February 17, 2025
Learn more
Blog


Key Components of Privileged Access Management Solutions
Privileged Access Management (PAM) solutions protect sensitive systems and data by managing privileged accounts through features like credential vaulting, automated password management, and session monitoring. PAM enforces strict access controls with multi-factor authentication, just-in-time access, real-time auditing, and role-based policies to minimize risks of unauthorized access and credential misuse, while supporting integration with existing IT infrastructure and enhancing compliance.
December 17, 2024
Learn more
Blog

%20and%20Its%20Importance.avif)
Understanding Privileged Access Management (PAM) and Its Importance
Privileged Access Management (PAM) protects critical systems from insider threats. Understand key components and best practices.
December 17, 2024
Learn more
Blog


Role of Identity and Access Management (IAM) in Cloud
Identity and Access Management (IAM) in the cloud provides critical security by managing and controlling user access to cloud resources, ensuring only authorized users can access sensitive data and applications. Cloud IAM offers benefits such as centralized access control across multiple cloud environments, granular privilege assignment, enhanced protection against breaches through strong authentication, improved regulatory compliance with auditing and reporting, and support for Zero Trust architectures, enabling organizations to balance security with operational flexibility and scalability
December 17, 2024
Learn more
Blog

IAM in Education: Managing Access for Students, Parents, and Staff
Identity and Access Management (IAM) in education secures access for students, parents, staff, and faculty by managing identities, authentication, and authorization while supporting compliance with data privacy regulations. IAM enhances digital learning by enabling seamless access to resources, streamlining administrative tasks, and protecting sensitive student and institutional data.
December 17, 2024
Learn more
Blog


IAM for Government: Securing Sensitive Data and Infrastructure
Identity and Access Management (IAM) in government secures sensitive data and infrastructure by enforcing strong user authentication, role-based access control, and continuous identity lifecycle management. Key IAM features like multi-factor authentication (MFA), privileged access management (PAM), and regulatory compliance reporting are vital to protecting national security, public health, and critical systems while enabling seamless government operations.
December 17, 2024
Learn more
Blog


IAM in e-Commerce: Balancing Security and User Experience
Identity and Access Management (IAM), including Customer Identity and Access Management (CIAM), is vital for retail and e-commerce businesses to balance robust security with seamless user experiences. IAM protects sensitive customer and employee data, ensures compliance with regulations like GDPR and PCI DSS, and enhances personalization through secure, unified access across multiple channels, enabling retailers to manage identities efficiently while reducing fraud and improving customer trust.
December 17, 2024
Learn more
Blog


IAM in Finance: Safeguarding Financial Transactions
Identity and Access Management (IAM) in financial services is critical for protecting sensitive data, securing transactions, and complying with strict regulations such as SOX, GLBA, GDPR, and PCI DSS. Key IAM features for finance include multi-factor authentication (MFA), role-based access control (RBAC), segregation of duties, user lifecycle management, behavioral monitoring, and comprehensive audit trails, all designed to prevent fraud, manage complex access policies, and support regulatory reporting while enabling seamless operational efficiency.
December 17, 2024
Learn more
Blog


IAM in Healthcare: Protecting Patient Data
Identity and Access Management (IAM) in healthcare protects sensitive patient data by enforcing role-based access control, multi-factor authentication, and continuous user activity monitoring. It supports regulatory compliance with HIPAA through detailed audit trails, automated user access reviews, and streamlined workflows, enhancing both security and operational efficiency in healthcare organizations.
December 17, 2024
Learn more
Blog


User Provisioning and De-Provisioning in Identity Access and Management
User provisioning and deprovisioning are vital for secure access control. Learn how Identity and Access Management (IAM) automates lifecycle management.
December 17, 2024
Learn more
Blog


The IAM Implementation Process: A Step-by-Step Guide
Implement Identity and Access Management (IAM) successfully with this step-by-step guide. Avoid common pitfalls and streamline deployment.
December 17, 2024
Learn more
Blog


Cloud Compliance and Regulatory Considerations: An Overview
Cloud Infrastructure Entitlement Management (CIEM) is essential for managing and controlling access rights in dynamic, multi-cloud environments. It enhances security by enforcing least privilege, providing continuous visibility into permissions, aiding compliance with regulations, and automating detection and remediation of excessive or risky access.
December 17, 2024
Learn more
Blog

%20in%20IAM.avif)
The Role of Single Sign-On (SSO) in IAM
Single Sign-On (SSO) enhances user experience and reduces password fatigue. Discover its role in secure Identity and Access Management (IAM) architecture.
December 17, 2024
Learn more
Blog

%20in%20CIEM.avif)
The Importance of Role-based Access Control (RBAC) in CIEM
Role-based access control (RBAC) strengthens security and simplifies compliance. Learn how RBAC fits into CIEM frameworks.
December 17, 2024
Learn more
Blog


7 Best Identity & Access Management (IAM) Solutions for 2024
Leading Identity and Access Management (IAM) solutions for 2024 include SailPoint, Saviynt, Okta, Ping Identity combined with ForgeRock, CyberArk, Microsoft Entra ID, and IBM Security Verify. These platforms excel in areas such as identity governance, cloud security integration, user-friendly access management, customer identity management, privileged access management, and compliance, providing scalable, flexible, and secure solutions tailored to diverse organizational needs and complexities.
December 17, 2024
Learn more
Blog


IAM and Compliance: Ensuring Regulatory Adherence
Identity and Access Management (IAM) systems are essential for meeting regulatory requirements like GDPR, HIPAA, SOX, and PCI DSS by enforcing strict control over user identities and access privileges. They support compliance through features such as multi-factor authentication, role-based access control, access reviews, audit logging, and automated provisioning to protect data integrity and enable efficient regulatory reporting.
December 17, 2024
Learn more
Blog


How IAM Helps Mitigate Cybersecurity Risks
Identity and Access Management (IAM) enhances cybersecurity by ensuring only authorized users access critical systems, helping prevent data breaches, ransomware spread, and insider threats. IAM also supports compliance with regulations, reduces human error through automation, and provides centralized control for managing user privileges, improving both security posture and operational efficiency.
December 17, 2024
Learn more
Blog


Components of Identity and Access Management (IAM) Systems
Identity and Access Management (IAM) systems consist of four key components: authentication, authorization, administration, and auditing/reporting. Authentication verifies user identities, authorization controls access levels, administration manages user accounts and permissions throughout their lifecycle, and auditing/reporting tracks user activity to ensure compliance and security.
December 17, 2024
Learn more
Blog


Why Identity and Access Management is So Important
Identity and Access Management (IAM) is the foundation of enterprise cybersecurity. Discover why identity is central to protecting digital assets.
December 17, 2024
Learn more
Blog

.avif)
Introduction to Identity and Access Management (IAM)
Identity and Access Management (IAM) is a cybersecurity framework that ensures the right individuals have appropriate access to organizational resources by managing digital identities and access permissions. It enhances security, streamlines operations through automation, and supports compliance by verifying identities, enforcing access controls, and monitoring user activities.
December 17, 2024
Learn more
Blog

Key Elements of Cloud Infrastructure Entitlement Management (CIEM)
Cloud Infrastructure Entitlement Management (CIEM) is a cybersecurity framework focused on managing and monitoring access permissions, or entitlements, within cloud environments. Key elements of CIEM include visibility into cloud entitlements, enforcing the principle of least privilege, using automated rightsizing of permissions, continuous monitoring with advanced analytics, centralized governance across multi-cloud environments, and compliance management to reduce security risks posed by excessive or misconfigured permissions.
December 17, 2024
Learn more
Blog

.avif)
Introduction to Cloud Infrastructure Entitlement Management (CIEM)
Cloud Infrastructure Entitlement Management (CIEM) is a security solution focused on managing and controlling identities, entitlements, and permissions within cloud and multi-cloud environments. CIEM helps organizations gain visibility into who has access to what, enforces the principle of least privilege, detects and corrects excessive or risky permissions, and supports compliance by continuously auditing entitlements to reduce the risk of data breaches and cloud misconfigurations.
December 17, 2024
Learn more
Blog

.avif)
The Role of Technology in Segregation of Duties (SoD): Automation, Software Solutions, and Analytics
Technology automates Segregation of Duties (SoD) for better compliance. See how analytics and Identity and Access Management (IAM) tools enforce policy.
December 17, 2024
Learn more
Blog

%20Definition%2C%20Importance%2C%20and%20Real-World%20Applications.avif)
Segregation of Duties (SoD): Definition, Importance, and Real-World Applications
Segregation of Duties (SoD), also known as Separation of Duties, is a fundamental internal control principle that divides critical business tasks among multiple individuals to prevent fraud, errors, and conflicts of interest by ensuring no single person has full control over a process. It enhances organizational security and accountability by creating checks and balances across key functions such as authorization, custody, recordkeeping, and reconciliation, and is a critical requirement in regulations like SOX, GDPR, and HIPAA.
December 17, 2024
Learn more
Blog


How CIAM Tools Collect and Use Customer Data to Enable Customer Lifecycle Management and Enhance the Customer Experience
CIAM tools collect customer data through account registration, user authentication (including device and location), user activity tracking, self-service updates, and integration with other systems like CRM and marketing platforms. This data supports personalized experiences, enhances security via fraud detection, ensures regulatory compliance with consent management, improves business offerings, and enables efficient customer lifecycle management through onboarding, profile management, engagement, and offboarding.
December 17, 2024
Learn more
Blog


Balancing Security and Customer Experience: The Role of CIAM
Consumer Identity and Access Management (CIAM) solutions help organizations strike a crucial balance between delivering seamless, personalized customer experiences and maintaining robust data security and privacy. By adopting passwordless authentication, multi-factor authentication, and effective consent management, CIAM reduces friction, enhances trust, and ensures compliance with evolving privacy regulations like GDPR and CCPA while securing customer data across digital interactions.
December 17, 2024
Learn more
Blog


Differences between CIAM and IAM Solutions
CIAM (Customer Identity and Access Management) and IAM (Identity and Access Management) both manage digital identities but serve different user bases and purposes. IAM focuses on controlling access for internal users like employees and contractors to protect organizational resources, emphasizing strict access controls and compliance. CIAM, on the other hand, manages external customer identities, prioritizing scalability, seamless user experiences, privacy compliance, and supporting diverse authentication methods such as social logins and consent management to cater to millions of users.
December 17, 2024
Learn more
Blog

.avif)
Benefits and Advantages of Customer Identity and Access Management (CIAM)
Customer Identity and Access Management (CIAM) solutions are vital for modern businesses focused on secure, seamless, and personalized customer experiences across digital channels. CIAM offers key benefits such as scalability to support millions of users, secure storage and tokenization of customer data, strong adaptive authentication including multi-factor and biometric methods, streamlined login and password reset processes, and comprehensive integration capabilities that enable consistent, compliant, and trustworthy digital customer interactions.
December 17, 2024
Learn more
Blog


Elevating the Customer Experience and Driving Business Growth with CIAM
Customer Identity and Access Management (CIAM) significantly elevates the customer experience by streamlining registration, enabling flexible authentication, and reducing friction throughout the user journey. By enhancing security with features like adaptive authentication and multi-factor authentication, CIAM builds customer trust, improves acquisition and retention, drives revenue through personalized marketing, reduces support costs, and mitigates security and fraud risks—all contributing to sustained business growth.
December 17, 2024
Learn more
Blog


Customer Identity and Access Management (CIAM): An In-Depth Overview
Customer Identity and Access Management (CIAM) is a specialized subset of Identity and Access Management focused on securely managing customer identities and access to digital services. Key components of CIAM include authentication methods like multi-factor and social login, authorization controls to enforce access rights, user profile management, single sign-on (SSO), consent management for privacy compliance, and threat detection to safeguard customer data while delivering seamless and personalized user experiences.
December 17, 2024
Learn more
Blog


Authentication vs Authorization for CIAM Tools
Authentication and authorization are distinct but complementary processes in identity and access management. Authentication verifies the identity of a user or system, typically through credentials like passwords, biometrics, or tokens, answering the question "Who are you?" Authorization determines what resources or actions the authenticated user is permitted to access, enforcing permissions based on roles, attributes, or policies. Authentication always precedes authorization, ensuring that only verified users receive appropriate access levels to protect sensitive data and systems.
December 16, 2024
Learn more
Blog


How People, Process, and Technology are Fundamental Elements of Modern Identity and Access Management (IAM) Programs
Modern Identity and Access Management (IAM) programs fundamentally consist of authentication, authorization, user lifecycle management, and identity governance. These components ensure secure verification of user identities, enforce appropriate access rights, manage users throughout their lifecycle, and provide oversight and compliance through auditing and reporting.
December 16, 2024
Learn more
Blog


7 Features to Consider When Evaluating PAM Vendors
When evaluating Privileged Access Management (PAM) vendors, organizations should consider key features including continuous scanning of privileged accounts for compliance, cross-cloud discovery for visibility across diverse environments, and just-in-time (JIT) or zero standing privilege access to minimize risk associated with persistent credentials. Additional important features are the ability to detect and prevent lateral movement, integration with ITSM and IGA platforms for streamlined access requests and auditability, and support for cloud and DevOps enablement to secure a broad range of privileged activities.
December 16, 2024
Learn more
Blog


Do You Need Zero Trust Security? 5 Signs the Model is Right for Your Organization
Five signs that indicate an organization may benefit from implementing Zero Trust security include lacking an existing Identity Access Management (IAM) system, having an IAM solution without a security perimeter, managing external users like contractors and vendors, enabling remote work on personal devices, and using SaaS or PaaS applications that require secure access controls. Zero Trust maximizes security by continuously verifying every user and device, enforcing least privilege access, and containing potential breaches through strict access controls and real-time monitoring.
December 16, 2024
Learn more
Blog


7 Benefits of Zero Trust Security for Enterprise
Implementing zero trust security provides enterprises with enhanced protection by continuously verifying users and devices, enforcing least-privilege access, and preventing lateral movement within networks. It also improves user experience through streamlined access, reduces IT operational burdens, supports digital transformation, offers greater visibility and monitoring, lowers security and compliance costs, and enables smarter, dynamic policy management for ongoing regulatory compliance.
December 16, 2024
Learn more
Blog

.avif)
Zero Trust isn’t Just for the Cloud. It Works for On-Premises, Too.
Zero Trust works beyond the cloud—on-premises too. See how this model strengthens hybrid infrastructure security.
December 16, 2024
Learn more
Blog

Improve Security with a Zero Trust Access Model
A Zero Trust access model assumes no implicit trust for any user, device, or network and requires continuous verification of identity and context before granting access. Its benefits include reducing the attack surface by enforcing least-privileged access, preventing lateral movement through network segmentation, improving detection and response with continuous monitoring, enhancing cloud and remote work security, and supporting regulatory compliance, all while improving user experience by reducing reliance on VPNs and enabling passwordless access options.
December 16, 2024
Learn more
Blog


What is Zero Trust? A Model for Effective Security
Zero Trust eliminates implicit trust and secures every access point. Learn the principles behind this modern security model.
December 16, 2024
Learn more
Blog


Differences between traditional, on-premises Privileged Access Management (PAM) versus modern PAM delivered as-a- service?
Traditional, on-premises Privileged Access Management (PAM) solutions are installed and managed within an organization's own infrastructure, offering greater control, customization, and compliance assurance but requiring significant maintenance, longer deployment times, and higher upfront costs. In contrast, modern cloud-based PAM solutions are delivered as a service (SaaS), providing faster deployment, scalability, reduced maintenance burden, and easier integration with cloud and hybrid environments, though they may introduce considerations like vendor lock-in and require adapting to cloud-native security models.
December 16, 2024
Learn more
Blog


Zero Trust - Definition, benefits, and is it the right methodology for you?
Zero Trust explained: a security model built on verification and least privilege. Understand its benefits for Identity and Access Management (IAM).
December 16, 2024
Learn more
Blog

How to Choose the Right CIAM Solution for Your Organization
A well-chosen CIAM solution secures customer identities while delivering seamless, personalized user experiences with features like multi-factor authentication, social login, and single sign-on. This webinar helps businesses evaluate key criteria such as scalability, security, integration, and compliance to select the best CIAM platform for their unique needs and growth goals.
December 12, 2024
Learn more
Blog


Discover the Best CIEM Solutions for Cloud Security
Leading CIEM solutions for cloud security include Authomize, CyberArk, Ermetic, Palo Alto Prisma Cloud, SailPoint, and Wiz, each offering strengths like real-time visibility, risk assessment, policy enforcement, and workload protection across multi-cloud environments. When choosing a CIEM platform, organizations should evaluate their specific needs, regulatory compliance requirements, cloud compatibility, core features such as AI-driven anomaly detection, scalability, user-friendliness, integration capabilities, vendor support, pricing, and conduct proof of concept testing to ensure the best fit for their cloud security posture.
December 12, 2024
Learn more
Blog


Role-Based Access Control (RBAC) in Identity and Access Management
Role-Based Access Control (RBAC) is a security framework that assigns system access based on a user’s role within an organization, ensuring users receive only the minimum permissions necessary to perform their job functions. RBAC simplifies access management by grouping users into roles linked to specific permissions, supports compliance through clear audit trails, and enhances security by reducing unauthorized access risks.
December 12, 2024
Learn more
Blog


A Comparative Analysis of Top IAM Tools
When selecting an Identity and Access Management (IAM) platform, organizations should consider how each solution aligns with their specific security requirements, infrastructure, and business needs. Leading IAM platforms like SailPoint, Saviynt, Okta, Ping Identity (with ForgeRock), CyberArk, Microsoft Entra ID, and IBM Security Verify vary in strengths such as governance, cloud integration, user experience, privileged access management, and scalability, making it essential to choose one that balances usability, compliance, and security for the organization’s unique environment.
December 12, 2024
Learn more
Blog

Segregation of Duties in Finance and Accounting
Segregation of Duties (SoD) in Finance and Accounting is a risk management principle that divides key financial tasks among different individuals to reduce the risk of error, fraud, and collusion. Examples include separating responsibilities such as approving vendor payments from reconciling bank statements, dividing the preparation and approval of financial reports, and ensuring those who handle cash receipts are not responsible for depositing or reconciling, thus creating a system of checks and balances that enhances financial integrity and accuracy.
December 12, 2024
Learn more
Blog

%20The%20Definitive%20Guide%20%5B2023%5D.avif)
Customer Identity and Access Management (CIAM): Implementation and Integration Best Practices
Successful Customer Identity and Access Management (CIAM) implementation involves selecting scalable solutions that balance security and user experience through flexible authentication methods and robust privacy controls. Integration into existing systems should be seamless, with ongoing monitoring and optimization to ensure compliance, security, and a smooth, personalized customer journey.
December 12, 2024
Learn more
Blog


Zero Trust Security and IAM: The Future of Access Control
Zero Trust and Identity and Access Management (IAM) redefine access control for modern enterprises. Explore how they work together to secure data.
December 12, 2024
Learn more
Blog


Identity Federation and Its Importance in Modern IAM
Federated identity is a system that links a single user identity across multiple separate identity management platforms, allowing seamless and secure access to various services with one login. It improves security, reduces IT overhead, enhances user experience by minimizing password fatigue, and supports compliance by providing a centralized view of access and activity across diverse systems.
December 12, 2024
Learn more
Blog


IAM Auditing and Monitoring: Ensuring Security and Compliance
IAM auditing and monitoring ensure security by tracking privileged access, detecting anomalies, and enforcing least privilege policies through regular reviews and session monitoring. Advanced solutions use real-time analytics and AI to understand user behavior, proactively preventing threats and ensuring compliance with evolving regulations.
December 12, 2024
Learn more
Blog

Preparing for the 2024 Solar Eclipse: A Guide to Implementing NIST CSF 2.0
The NIST Cybersecurity Framework (CSF) 2.0 provides a structured, phased approach to managing cybersecurity risk, featuring six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. Implementation involves prioritizing assets and risks, creating current and target profiles, performing risk assessments, identifying and addressing gaps, and continuously monitoring and improving cybersecurity posture, supported by guidance and tools for practical application across organizations of all sizes.
December 12, 2024
Learn more
Blog

Five Common IGA Challenges and How Managed Services Can Help Solve Them
Identity Governance and Administration (IGA) tools face common challenges including lack of internal expertise, difficulty justifying ROI, onboarding applications at scale, automating manual processes, and managing third-party identities securely. Managed service providers help address these by providing skilled resources on demand, accelerating application integration, implementing automation to reduce manual effort, and ensuring scalable, secure third-party identity management to improve compliance and operational efficiency.
December 12, 2024
Learn more
Blog


Navigating the Challenges and Mitigation Strategies of Segregation of Duties
Segregation of Duties (SoD) is a critical internal control mechanism that reduces the risk of fraud and errors by ensuring no single individual has control over all aspects of a critical process. Key challenges in implementing SoD include lack of awareness, technological complexity, resource limitations, and resistance to change, which can be mitigated through clear role definitions, continuous monitoring, automation, stakeholder involvement, and strategic use of identity governance tools to maintain effective and compliant SoD controls.
December 12, 2024
Learn more
Blog

%20%20An%20In-Depth%20Overview.avif)
Customer Identity and Access Management (CIAM) Use Cases: An In-Depth Overview
Customer Identity and Access Management (CIAM) is used across industries to enhance customer experiences and secure digital interactions. Common use cases include personalized experiences and fraud prevention in retail and e-commerce, streamlined KYC and compliance in financial services, secure patient identity management in healthcare, frictionless onboarding in travel and hospitality, and unified customer profiles in telecommunications.
December 12, 2024
Learn more
Blog


Key Components and Features of a Successful CIAM Program
A successful Customer Identity and Access Management (CIAM) program includes key features such as self-service registration and account management, single sign-on (SSO), multi-factor authentication (MFA), a centralized customer directory, and developer tools like APIs and SDKs for seamless integration. Essential components also involve advanced frictionless security, strong privacy management, API integration, data access control, compliance adherence, customer analytics, scalability, and an enhanced overall customer experience to ensure secure, seamless, and personalized interactions.
December 12, 2024
Learn more
Blog


Customer Identity and Access Management (CIAM): The Definitive Guide
Customer Identity and Access Management (CIAM) is a specialized solution designed to securely manage and authenticate external customer identities, providing seamless and personalized digital experiences while ensuring compliance with privacy regulations. Key components of CIAM include authentication methods (passwords, biometrics, MFA), authorization controls like Role-Based Access Control (RBAC), user profile and consent management, Single Sign-On (SSO), data privacy enforcement, and integration with emerging technologies such as AI and blockchain to enhance security, fraud detection, and identity verification.
December 12, 2024
Learn more
Blog


Cloud Entitlement Discovery and Inventory: Navigating Access Control in the Cloud
Cloud Infrastructure Entitlement Management (CIEM) helps organizations manage and control cloud access by providing continuous visibility into entitlements, automating least-privilege enforcement, and detecting risks across multi-cloud environments. This centralized approach improves security, ensures compliance, reduces excessive permissions, and streamlines audit readiness within dynamic cloud infrastructures.
December 12, 2024
Learn more
Blog


NYDFS Amendment User Access Reviews
The New York Department of Financial Services (NYDFS) amended its 23 NYCRR Part 500 cybersecurity regulation to require financial institutions to conduct annual User Access Reviews (UARs) focusing on access privileges and management. These regulations, effective May 1, 2025, mandate limiting and reviewing user access, promptly disabling unnecessary accounts, securing remote access protocols, and implementing strong password policies to mitigate risk and enhance compliance.
December 12, 2024
Learn more
Blog


Biometric Authentication and IAM: A Secure and User-Friendly Approach
Biometric authentication in Identity and Access Management (IAM) enhances security by using unique biological traits such as fingerprints or facial recognition to verify user identities, offering a more secure and user-friendly alternative to traditional passwords. It supports various methods like fingerprint scanning, iris recognition, and voice identification, and is increasingly adopted across industries despite challenges related to privacy, regulatory compliance, and potential biases, requiring organizations to implement strong data protection and ethical guidelines.
December 12, 2024
Learn more
Blog


The Impact of Artificial Intelligence and Machine Learning on IAM
Artificial intelligence (AI) and machine learning (ML) are revolutionizing Identity and Access Management (IAM) strategies. Explore predictive access and intelligent threat detection.
December 12, 2024
Learn more
Blog


Choosing the Perfect IAM Solution: A Step-by-Step Guide for Your Organization
Choosing the right Identity and Access Management (IAM) solution involves a thorough, multi-step process that begins with assessing an organization’s specific requirements, including user authentication, compliance, and privileged access management needs. Evaluating the IT environment for integration compatibility and scalability, considering security features aligned with regulatory standards, and prioritizing user experience and accessibility are essential.
December 12, 2024
Learn more
Webinar


Transforming Identity Security for Higher Education: Microsoft Entra Suite Demonstration
Transforming Identity Security for Higher Education: Microsoft Entra Suite Demonstration
Discover practical identity modernization paths using Microsoft Entra Suite and HorizonID.
March 5, 2026
Webinar


Preparing for Life After MIM: Modernizing Identity with Microsoft Entra ID Governance
Preparing for Life After MIM: Modernizing Identity with Microsoft Entra ID Governance
Is your organization prepared for the end of MIM? Now is the time to start planning.
February 24, 2026
Data Sheet


Migrate to Microsoft Entra ID: Readiness & Roadmap Quick Start
Migrate to Microsoft Entra ID: Readiness & Roadmap Quick Start
Assess your current IAM environment and establish a practical roadmap for moving to Microsoft Entra ID with this focused advisory engagement.
February 10, 2026
Data Sheet


MIM-to-Microsoft Entra Readiness & Roadmap Quickstart
MIM-to-Microsoft Entra Readiness & Roadmap Quickstart
Assess your current Microsoft Identity Manager (MIM) setup and plan a clear migration path to Microsoft Entra ID.
February 10, 2026
Data Sheet


Turning Rust into Resilience: Active Directory Consolidation
Turning Rust into Resilience: Active Directory Consolidation
Restore strength and agility by transforming outdated, fragmented Active Directory environments into a resilient, cloud-first foundation with Microsoft Entra ID.
February 10, 2026
Data Sheet


Less Friction, More Flow: Migrating from Okta to Microsoft Entra ID
Less Friction, More Flow: Migrating from Okta to Microsoft Entra ID
Plan your migration from Okta to Microsoft Entra to simplify your identity stack without compromising security.
February 10, 2026
Data Sheet


47-Day Certificate Automation Readiness Checklist
47-Day Certificate Automation Readiness Checklist
A readiness checklist to help organizations prepare for 47‑day TLS certificate lifespans through automated discovery, ownership, renewal, and monitoring.
January 26, 2026
White Paper


Modernize Your Privileged Access Management Program
Modernize Your Privileged Access Management Program
A concise guide to modernizing PAM to reduce identity‑based risk, improve operational efficiency, and secure high‑risk access across cloud and on‑prem environments.
January 26, 2026
White Paper


NomadID: Mission-Ready Identity Management for Federal Agencies in DDIL Scenarios
NomadID: Mission-Ready Identity Management for Federal Agencies in DDIL Scenarios
NomadID is a highly mobile, compact ICAM solution that can be quickly deployed and utilized in tactical and edge environments.
December 18, 2025
White Paper


Building Digital Trust: How IDProof+ Secures Remote Hiring, Contractor Access, and Call Centers
Building Digital Trust: How IDProof+ Secures Remote Hiring, Contractor Access, and Call Centers
Discover how IDProof+ ensures identity assurance, mitigates risks, and delivers trusted business security.
December 17, 2025
Data Sheet


MajorKey Federal Capabilities Overview: Securing Federal Identities with Trusted Expertise
MajorKey Federal Capabilities Overview
MajorKey and its affiliates deliver trusted identity services and solutions for federal organizations.
December 8, 2025
Data Sheet


NomadID Overview: Mission-Ready Identity Management for Federal Agencies in DDIL Scenarios
NomadID Overview: Mission-Ready Identity Management for Federal Agencies in DDIL Scenarios
NomadID delivers mission-ready identity management for federal agencies operating in disconnected, denied, intermittent, and low-bandwidth (DDIL) environments. By ensuring uninterrupted authentication and single sign-on at the tactical edge, it enhances security, resilience, and operational continuity—even under the most challenging conditions.
December 8, 2025
Data Sheet


Leveraging AI in Identity Security Overview
Leveraging AI in Identity Security Overview
Navigate AI opportunities and risks through the lens of identity security.
November 18, 2025
Data Sheet


Microsoft Copilot: AI Readiness Advisory Assessment
Microsoft Copilot: AI Readiness Advisory Assessment
Ensure responsible Microsoft Copilot adoption for improved identity security.
November 18, 2025
Data Sheet


Microsoft Entra Suite Workshop
Microsoft Entra Suite Workshop
Discover the robust and comprehensive identity and security capabilities of Microsoft Entra.
November 10, 2025
Webinar


From Legacy to Legendary: Reinvent IAM with HorizonID and Microsoft Entra
From Legacy to Legendary: Reinvent IAM with HorizonID and Microsoft Entra
Break free from outdated identity tools and accelerate your journey to a modern, secure, and fully automated identity ecosystem with HorizonID and Microsoft Entra Suite.
November 3, 2025
White Paper


IdentityLens: Real-Time Visibility and Analytics for Your Entire Identity Ecosystem
IdentityLens: Real-Time Visibility and Analytics for Your Entire Identity Ecosystem
Unlock smarter, faster decisions with real-time analytics and complete visibility into your identity ecosystem
October 28, 2025
Webinar


PAM Automation Playbook: Identifying Quick Wins and Strategic Gains
PAM Automation Playbook: Identifying Quick Wins and Strategic Gains
This session offers practical guidance on identifying automation opportunities, achieving quick wins, and building stakeholder support.
October 28, 2025
Data Sheet


Improve Security Without Compromising the Pace of Care
Identity That Works for Healthcare
The Access Experience Assessment helps healthcare organizations transform their clinician's digital experience.
October 20, 2025
Data Sheet


HorizonID: The Bridge Between Legacy and Modern Identity
HorizonID Overview
HorizonID is designed to enhance Microsoft Entra Suite by enabling a smooth transition of complex integrations
October 6, 2025
Data Sheet


IDProof+ Overview: High-Assurance Identity Verification
IDProof+ Overview
IDProof+ uses advanced identity validation to verify users against government-issued IDs
October 3, 2025
Data Sheet


Identity Advisory Services
Identity Advisory Services
MajorKey delivers end-to-end advisory, integration, and managed services tailored specifically for Ping Identity clients to accelerate platform adoption and maximize investment value. Specializing in complex deployments, customizations, and continuous program enhancement, MajorKey ensures seamless integration, automation, and compliance across workforce IAM, PAM, and CIAM, enabling organizations to reduce risk, improve operational efficiency, and achieve faster time-to-value.
September 25, 2025
Success Story


Recovering a CyberArk Implementation for a Healthcare FinTech Leader
Recovering a CyberArk Implementation for a Healthcare FinTech Leader
Learn how MajorKey helped a healthcare technology company overcome a stalled CyberArk implementation to achieve full PAM adoption.
September 25, 2025
Success Story


Transforming Privileged Access Management with CyberArk
Transforming Privileged Access Management with CyberArk
Modernizing privileged access management for a public sector technology team
September 24, 2025
White Paper


Powering Business Resilience Through Identity Security and Service Management
Powering Business Resilience Through Identity Security and Service Management
Integrating identity security with service management and AI empowers organizations to build resilient, scalable enterprises that maintain secure access and streamline operations in a cloud-first world. This approach enables faster threat detection, automated access decisions, and seamless compliance, ensuring business continuity and operational excellence amid evolving risks and regulatory demands.
September 19, 2025
Success Story


A Modern, Scalable IGA Solution for a Large Healthcare Network
A Modern, Scalable IGA Solution for a Large Healthcare Network
Migrating to Microsoft Entra ID Governance to consolidate identity and security solutions for reduced risk and streamlined processes.
September 19, 2025
Success Story


Migrating an East Coast Healthcare Non-Profit to Microsoft Entra ID Governance
Consolidating Identity Processes, Improving Security, and Reducing Costs with Microsoft Entra ID Governance
For healthcare organizations, Microsoft Entra ID Governance provides an opportunity to consolidate identity management processes, improve security, and reduce IT infrastructure costs.
September 19, 2025
Success Story


Improving Security with Microsoft 365 Security Services for a Large Community College System
Helping Community Colleges Improve Security with Microsoft 365 Security Services
Enabling robust and evolving security solutions with Microsoft Entra ID and Microsoft 365 Security Services for a large network of community colleges.
September 19, 2025
Success Story


Implementing Saviynt EIC for a Large Apparel Retailer
Streamlining Access Reviews and Identity Governance with Saviynt EIC for a Large Retailer
A large apparel retailer partnered with Oxford Computer Group, a MajorKey Technologies Company, to help lay the foundation for a robust identity governance infrastructure.
September 19, 2025
Success Story


Streamlining Identity and Access Management Post Acquisition
Identity Integration and Consolidation Post Acquisition
Oxford Computer Group, a MajorKey Technologies company, developed and implemented a streamlined template for integrating identity systems after acquisitions.
September 19, 2025
Success Story


Migrating to Microsoft Entra ID for a Zero Trust, Cloud-First Future
Saying Goodbye to ADFS: Migrating a Federal Agency to Microsoft Entra ID for a Zero Trust, Cloud-First Future
A large federal agency successfully migrated from ADFS to Microsoft Entra ID, streamlining identity management for 480 applications and strengthening security with conditional access policies. This cloud-first transformation reduced complexity, improved reliability, and positioned the agency for a Zero Trust future.
September 19, 2025
Success Story


Retailer Updates Separation of Duty Rulesets to Maintain SOX Compliance
Retailer Updates Separation of Duty Rulesets to Maintain SOX Compliance
MajorKey updated the client's FastPath instance to help them pass SOX audit and find maximum value following changes to their internal business processes.
July 25, 2025
Success Story

Top Ranked Children's Hospital Automates New User Processing
Top Ranked Children's Hospital Automates New User Processing - Saving 2,600 Hours Provisioning New Users Annually
The MajorKey team fully automated the user creation process with SailPoint IdentityIQ, saving 2,600-man hours annually while reducing security risks.
July 24, 2025
Success Story


Reservation Service Gains Cloud Visibility and a Least-Privilege Identity Strategy
Online restaurant-reservation service gains cloud visibility and a least-privilege identity strategy
Over-privileged accounts and lack of visibility lead to increased security risk and possible increased cloud costs.
July 24, 2025
Success Story


Mitigating risk exposure while reducing process time with user non-starts
Supply Chain Company Mitigates Risk Exposure and Reduces Process Time by Automating User Non-Starts Instantly
The customer was experiencing significant inefficiencies around governing user non-starts. Due to the manual nature of their process, every non-start would take several days to complete.
July 24, 2025
Success Story


Rescuing Stalled FastPath Deployment at a Food & Beverage Manufacturer
Rescuing Stalled FastPath Deployment at a Food & Beverage Manufacturer
The client was running into issues with their FastPath implementation partner and struggling to make progress until MajorKey got it over the finish line.
July 24, 2025
Success Story


Helping a Multinational Insurance Company Implement Saviynt
Helping a Multinational Insurance Company Implement Saviynt
MajorKey successfully implemented Saviynt for a multinational insurance company, supporting the adoption of an IGA program built on best practices. Their approach streamlined identity lifecycle management, improved compliance, and reduced operational risks while maximizing the client’s Saviynt investment.
July 24, 2025
Success Story


Helping a Fortune 500 Bank Get SailPoint Back on Track
Helping a Fortune 500 Bank Get SailPoint Back on Track
MajorKey rescued a stalled SailPoint implementation at a Fortune 500 bank after two previous integrators failed to deliver, resolving key configuration issues and streamlining application onboarding. Their program-level approach enabled onboarding hundreds of applications simultaneously, saving significant time and resources while restoring client confidence.
July 24, 2025
Success Story


Advising and Implementing Governance to Help Customer Go Public
Advising and Implementing Governance to Help Customer Go Public
MajorKey helped a global food and beverage manufacturer establish Application Governance controls to meet SOX requirements in order to go public.
July 24, 2025
Success Story


Guiding a Global Manufacturer Through IGA Modernization
Guiding a Global Heavy Equipment Manufacturer Through IGA Modernization
MajorKey fast-tracked the vendor selection and implementation process to modernize a global heavy equipment manufacturer’s identity and application governance program. Their work streamlined SAP security controls, automated access requests, and enabled zero-day user starts, helping the client achieve compliance, reduce risks, and improve operational efficiency.
July 24, 2025
Success Story


Accelerating New User Onboarding at a Major US Municipal Hospital System
From Three Days to Three Minutes: Accelerating New User Onboarding at a Major US Municipal Hospital System
MajorKey accelerated user onboarding and offboarding at a major US municipal hospital system from days to minutes by fully automating the processes. This transformation improved operational efficiency, enhanced security by reducing risk exposure, and enabled the healthcare organization to scale identity access management with confidence.
July 24, 2025
White Paper

Fundamentals of Customer Identity and Access Management (CIAM)
Fundamentals of Customer Identity and Access Management (CIAM)
Customer Identity and Access Management (CIAM) enables organizations to securely manage customer identities and data while delivering seamless and personalized digital experiences. It encompasses user registration, multifactor authentication, consent and preference management, and dynamic authorization, ensuring strong security and compliance with privacy regulations while enhancing customer trust and engagement.
July 23, 2025
White Paper


CIAM Solutions Buyer's Guide
CIAM Solutions Buyer's Guide
Choosing the right CIAM platform means balancing security, scalability, and user experience to protect customer identities. This guide compares five leading solutions—CyberArk, ForgeRock, Microsoft, Ping Identity, and Okta—helping organizations match technology to business goals.
July 23, 2025
White Paper


Identity and Access Management Buyer’s Guide
Identity and Access Management Buyer’s Guide
A business-driven approach to Identity and Access Management (IAM) improves IT and line-of-business collaboration, streamlines implementations, and enhances enterprise security and user experience. Following best practices and a four-step strategy helps ensure successful IAM programs that meet organizational needs and reduce frustrations.
July 23, 2025
Identicast


Ep. 3 – The Convergence of App Governance and Identity Security with Delinea
Ep. 3 – The Convergence of App Governance and Identity Security with Delinea
We discuss the convergence of application governance and identity security with Frank Vukovits of Delinea.
July 23, 2025
Identicast


Data Sheet


SkyDock: CyberArk Migration Tool
SkyDock
SkyDock is a specialized migration tool from MajorKey designed to automate and simplify migrations between CyberArk environments, including on-premises to Privilege Cloud or internal instance transfers. It ensures data integrity and security by using REST API connections, threaded processing for speed, secure secret handling without persistence, flexible object migration, permission mapping, detailed logging for compliance, and error management with retry and rollback capabilities.
July 23, 2025
Data Sheet


SailPoint Managed Services Provider Offers
SailPoint Managed Services Provider Offers
MajorKey’s SailPoint Managed Services program provides end-to-end administrative control and strategic advisory to optimize SailPoint Identity Security Cloud investments. Offering flexible service tiers, MajorKey accelerates integrations and adoption, manages ongoing operations, and ensures compliance with global best practices to maximize efficiency, security, and business value.
July 23, 2025
Data Sheet


SailPoint IIQ to ISC migration programs
SailPoint IIQ to ISC migration programs
Migrating from SailPoint IdentityIQ to SailPoint Identity Security Cloud (ISC) enables organizations to reduce operational overhead, gain AI-driven insights, and accelerate cloud adoption with continuous, seamless updates. MajorKey guides clients through this transformation by cleaning up legacy customizations, streamlining workflows, and deploying best practices to maximize security, scalability, and ROI.
July 23, 2025
Data Sheet


OrchestratID: Automate Any Task
OrchestratID
OrchestratID is a low-code identity orchestration platform that automates and standardizes complex identity and access workflows across hybrid and multi-cloud environments. By integrating diverse identity providers and business applications, it streamlines user onboarding, authentication, policy enforcement, and lifecycle management—reducing manual tasks, enhancing security, and enabling rapid, code-free process automation.
July 23, 2025
Data Sheet


CredSafe: CyberArk Credential Recovery Tool
CredSafe
CredSafe ensures seamless access to critical privileged credentials during CyberArk outages or maintenance. It integrates with CyberArk’s Central Credential Provider (CCP) to provide real-time, auditable credential access without compromising security or compliance, minimizing operational disruption in mission-critical environments.
July 23, 2025
Data Sheet


Optimize your Saviynt platform with MajorKey experts
Optimize your Saviynt platform with MajorKey experts
MajorKey maximizes the value of Saviynt's identity governance platform by helping customers deploy, optimize, and continuously improve their identity security investments. The collaboration delivers advisory, integration, and managed services designed to enhance security, operational efficiency, and business growth while balancing robust protection with user convenience.
July 23, 2025
Data Sheet


Data Sheet


Methodology for a successful PAM program with CyberArk
Methodology for a successful PAM program with CyberArk
CyberArk Privileged Access Management (PAM) solutions secure, control, and monitor privileged accounts to reduce risk and enhance compliance across hybrid and multi-cloud environments. Key capabilities include zero standing privileges, session isolation, threat detection, automated credential management, and secure third-party access, all designed to strengthen security and operational efficiency.
July 23, 2025
Data Sheet


Deploying and integrating SailPoint ARM
Deploying and integrating SailPoint ARM
SailPoint ARM (Access Risk Management) enables organizations to prevent segregation of duties (SoD) violations and reduce fraud risks without hampering productivity. MajorKey provides advisory, integration, and managed services to help clients implement effective SoD programs, continuous control monitoring, and automated compensating controls for hybrid environments, including SAP and other financial applications.
July 23, 2025
Data Sheet


Authenticate, Administer, Authorize, and Audit with Ping Identity
Authenticate, Administer, Authorize, and Audit with Ping Identity
MajorKey provides Ping Identity advisory, integration, and managed services, delivered through its highly skilled teams of onshore, nearshore, and offshore resources.
July 23, 2025
Data Sheet


Control your non-employee identities with MajorKey and SailPoint NERM
Control your non-employee identities with MajorKey and SailPoint NERM
SailPoint NERM (Non-Employee Risk Management) helps organizations efficiently manage and safeguard non-employee identities such as contractors, partners, and vendors. MajorKey delivers advisory and managed services around SailPoint NERM to provide visibility into non-employee access, enforce compliance, automate provisioning and remediation, and mitigate costly third-party breach risks.
July 23, 2025
Webinar


Who Gives a Sh*t About Identity Security – How to Create Business Value from IAM
Who Gives a Sh*t About Identity Security – How to Create Business Value from IAM
Identity and Access Management (IAM) programs create business value by streamlining secure user access, reducing risks such as credential theft, and improving operational efficiency across departments. By defining common business outcomes and building leadership support, organizations can protect budgets, foster program champions, and leverage AI to enhance IAM’s impact on HR, marketing, and other teams, driving meaningful organizational transformation.
July 23, 2025
Webinar


Understanding Privileged Access Management (PAM)
Understanding Privileged Access Management (PAM)
Privileged Access Management (PAM) is essential for protecting organizations against data breaches by controlling, monitoring, and securing privileged accounts with just-in-time, least privilege access. This webinar provides an overview of PAM and Privileged Identity Management (PIM), covering use cases, compliance support, and solution capabilities like Saviynt CPAM and Microsoft Entra ID PIM to strengthen cybersecurity posture effectively.
July 23, 2025
Webinar


Using Microsoft Entra Verified ID for Identity Proofing of Partners, Customers, and Employees
Using Microsoft Entra Verified ID for Identity Proofing of Partners, Customers, and Employees
Microsoft Entra Verified ID enables continuous, secure identity proofing for partners, customers, and employees across hybrid work and distributed environments. This webinar explores common use cases such as onboarding and help-desk verification, explaining how Verified ID enhances security by validating identity attributes and roles with verifiable credentials.
July 23, 2025
Webinar


Transform Your Security Strategy with Microsoft Sentinel and a Modern Managed SOC
Transform Your Security Strategy with Microsoft Sentinel and a Modern Managed SOC
Enhance your organization's security posture with Microsoft Sentinel, a cloud-native SIEM powered by AI and automation, integrated with Microsoft Defender and Entra ID signals. This webinar demonstrates how a modern Security Operations Center (SOC) with 24x7 monitoring can provide improved threat detection, faster response times, and comprehensive digital estate protection.
July 23, 2025
Webinar


Transitioning from the MIM Portal to Microsoft Entra ID: MIM Retirement Series Part 2
Transitioning from the MIM Portal to Microsoft Entra ID: MIM Retirement Series Part 2
Modernize your identity strategy by transitioning from the Microsoft Identity Manager (MIM) Portal to Microsoft Entra ID while maintaining existing on-premises synchronization with the MIM sync engine. This webinar explores how to leverage Entra ID’s advanced self-service, automated workflows, and governance capabilities without disrupting hybrid environments, featuring practical guidance and real-world migration examples.
July 23, 2025
Webinar


The Rise of AI Threats: Identity Management
The Rise of AI Threats: Identity Management
Explore how artificial intelligence is creating new and sophisticated threats to identity management systems and discover strategies to mitigate these risks. This webinar examines AI-enabled impersonation techniques, deepfake risks, and how cybercriminals leverage AI, along with practical steps organizations can take to protect identities in an evolving threat landscape.
July 23, 2025
Webinar


The Great Convergence: Bridging the Gap Between Identity and App Governance
The Great Convergence: Bridging the Gap Between Identity and App Governance
Discover how the identity and application governance vendor landscape is evolving amid rapid market convergence. This webinar explores best practices for extending SoD frameworks to ERP and cloud environments, managing role remediation, and integrating application governance with privileged access management to optimize business services.
July 23, 2025
Webinar


Securing Academic Partnerships: Overcoming Identity Challenges in Collaborative Higher Education Environments
Securing Academic Partnerships: Overcoming Identity Challenges in Collaborative Higher Education Environments
Secure seamless collaboration across universities and research partners by addressing identity challenges in higher education environments. This webinar explores strategies to protect sensitive data, manage diverse access systems, ensure compliance, and support scalable, secure academic partnerships using modern identity solutions.
July 23, 2025
Webinar


Navigating the Future of Identity: 2024 Year End Review & Top Predictions for 2025
Navigating the Future of Identity: 2024 Year End Review & Top Predictions for 2025
Explore the most impactful advances in Identity Access Management (IAM), governance, and security from 2024, and prepare for the top five identity management trends shaping 2025. This webinar delivers expert insights on overcoming challenges, enhancing compliance, and leveraging emerging technologies like AI to future-proof your organization's identity strategy.
July 23, 2025
Webinar


Moving from MIM to Microsoft Entra ID Governance to Future Proof Identity Management
Moving from MIM to Microsoft Entra ID Governance to Future Proof Identity Management
Transition from Microsoft Identity Manager (MIM) to Microsoft Entra ID Governance to enhance security, streamline identity processes, and future-proof your identity management strategy. This webinar details key benefits, customer experiences, and practical migration guidance to help organizations modernize IAM with a scalable and cloud-native governance solution.
July 23, 2025
Webinar


Moving MIM Group Functionality to Azure AD for On-Premises Group Attestation
Moving MIM Group Functionality to Azure AD for On-Premises Group Attestation
Azure AD Group Writeback enables syncing of Azure AD groups to on-premises Active Directory, reducing reliance on Microsoft Identity Manager (MIM) and streamlining group management. This webinar covers how to move MIM group functionality to Azure AD, improve compliance through attestation, and simplify group approvals, workflows, and entitlement management for a zero trust security approach.
July 23, 2025
Webinar


Migrating from ADFS to Azure Active Directory: Benefits and Best Practices
Migrating from ADFS to Azure Active Directory: Benefits and Best Practices
Migrate from ADFS to Microsoft Entra ID to enhance your security posture, reduce IT costs, and streamline user access to thousands of apps. This webinar covers the benefits and best practices for a smooth migration, including improved risk management, compliance, and a unified cloud-based identity control plane that simplifies sign-on experiences.
July 23, 2025
Webinar


Maximizing Value, Showcasing Success, and Future-Proofing Your Identity Program
Maximizing Value, Showcasing Success, and Future-Proofing Your Identity Program
Maximize the value of your identity program and showcase its business impact to leadership for sustained budget support. This on-demand webinar reveals five key strategies to accelerate time to value, improve compliance performance, and future-proof your identity program against market disruptions and evolving challenges.
July 23, 2025
Webinar


Migrating from MIM Sync: User Provisioning with Microsoft Entra ID
Migrating from MIM Sync: User Provisioning with Microsoft Entra ID
Migrate user provisioning from Microsoft Identity Manager (MIM) Sync to Microsoft Entra ID for a secure, scalable, and cloud-native identity management solution. This webinar covers migration strategies, automation using SCIM and HR-driven provisioning, auditing capabilities, and best practices for seamless user lifecycle management across hybrid and cloud environments.
July 23, 2025
Webinar


How to Get the Most Out of Your Microsoft 365 Investments
How to Get the Most Out of Your Microsoft 365 Investments
Maximize the value of Microsoft 365 investments by leveraging the full capabilities of Microsoft Entra and Azure AD. Gain insights on reducing licensing costs, streamlining IT operations, and strengthening cloud security by optimizing identity lifecycle management and governance workflows.
July 23, 2025
Webinar


Machine Identities: Uncovering the Hidden Risks in your Environment
Machine Identities: Uncovering the Hidden Risks in your Environment
Uncover the hidden risks posed by machine identities in your IT environment and learn strategies to manage their security effectively. This webinar dives into the challenges of discovering, governing, and protecting machine identities to reduce attack surfaces and prevent unauthorized access in modern enterprises.
July 23, 2025
Webinar


Introduction to Microsoft’s Security Service Edge for Identity-Centric Network Access
Introduction to Microsoft’s Security Service Edge for Identity-Centric Network Access
Unlock seamless, secure access to apps and resources anywhere with Microsoft's identity-centric Security Service Edge (SSE) solution, integrating Entra Internet Access, Entra Private Access, and Defender for Cloud Apps. This webinar explores how unified Conditional Access policies and Zero Trust principles streamline network security while enhancing user experience for modern cloud and mobile workforces.
July 23, 2025
Webinar


How to Demonstrate Success and Grow the ROI of CIAM Programs
How to Demonstrate Success and Grow the ROI of CIAM Programs
Successful CIAM programs drive revenue growth by improving customer experiences and protecting against fraud. Measuring CIAM success involves tracking key metrics such as user adoption, conversion rates, security incident reduction, and leveraging analytics to optimize the customer journey and demonstrate business value.
July 23, 2025
Webinar


How Misconfigured Hybrid Identity Setups Can Compromise Cybersecurity
How Misconfigured Hybrid Identity Setups Can Compromise Cybersecurity
Misconfigured hybrid identity systems, including Microsoft Entra ID and on-premises Active Directory, can increase an organization's vulnerability to cyberattacks by exposing complex and legacy setups. This webinar highlights common blind spots such as synced service accounts and federated identity services, while offering best practices to simplify authentication, enforce least privilege, and secure hybrid identity environments.
July 23, 2025
Webinar


How to Bolster Security and Create Business Value Through Third-Party IAM
How to Bolster Security and Create Business Value Through Third-Party IAM
Extending Identity and Access Management (IAM) to third parties and non-employees enhances security while unlocking business value through streamlined vendor lifecycle, delegated administration, and relationship management. Learn strategies to address governance, audit requirements, and stakeholder engagement for a successful third-party IAM program.
July 23, 2025
Webinar


Fortifying Your Cyber Defenses: Using Microsoft Defender to Prevent Token Theft and AiTM Attacks
Fortifying Your Cyber Defenses: Using Microsoft Defender to Prevent Token Theft and AiTM Attacks
Explore strategies to defend against token theft and adversary-in-the-middle (AiTM) attacks using Microsoft Defender and Sentinel. It covers attack mechanics, their impact, and demonstrates detection and response techniques to enhance an organization’s cybersecurity posture.
July 23, 2025
Webinar


From SailPoint IdentityIQ to Identity Security Cloud: Creating Value with Cloud
From SailPoint IdentityIQ to Identity Security Cloud: Creating Value with Cloud
Migrating from SailPoint IdentityIQ to Identity Security Cloud (ISC) offers significant benefits including reduced total cost of ownership, faster deployment, continuous updates with no downtime, and AI-driven security insights. This migration leverages existing investments while enabling scalable, cloud-native identity security that enhances visibility, risk detection, and operational efficiency.
July 23, 2025
Webinar


Creating Transformative Identity Governance Solutions with Microsoft Entra Suite
Creating Transformative Identity Governance Solutions with Microsoft Entra Suite
HorizonID extends Microsoft Entra ID Governance by resolving legacy integration challenges and simplifying complex identity workflows. This webinar highlights how HorizonID accelerates identity modernization, improves data reconciliation, and helps organizations fully leverage their Microsoft Entra investment.
July 23, 2025
Webinar


Exploring Microsoft's Security Service Edge (SSE) Solution
Exploring Microsoft's Security Service Edge (SSE) Solution
Microsoft’s Security Service Edge (SSE) delivers unified, cloud-based security by integrating identity-aware network access, Zero Trust Network Access, Secure Web Gateway, and Cloud Access Security Broker capabilities. It replaces legacy VPNs with seamless, secure global access while eliminating security gaps and simplifying access control management for modern distributed workforces.
July 23, 2025
Webinar


Discover the Microsoft Entra Suite: Unlocking Unified Identity and Access Management
Discover the Microsoft Entra Suite: Unlocking Unified Identity and Access Management
Microsoft Entra Suite offers a unified, advanced solution for managing identity and access, ensuring secure access to critical systems while protecting sensitive data and ensuring compliance. This webinar covers tailored identity workflows for new hires, role changes, and exits, fraud prevention through identity proofing, secure hybrid work scenarios, and integration with platforms like Epic and Workday.
July 23, 2025
Webinar


Demystifying Modern Authentication
Demystifying Modern Authentication
Modern authentication provides powerful tools for securing user identities and managing access, but its complexity can be challenging. This webinar demystifies modern authentication, explaining key components, benefits, security processes, and how Microsoft’s solutions support a smooth authentication journey.
July 23, 2025
Webinar


Control your Cloud: Mastering Least Privilege with CIEM
Control your Cloud: Mastering Least Privilege with CIEM
Cloud Infrastructure Entitlement Management (CIEM) helps establish and maintain least privilege across multi-cloud environments by providing centralized visibility and control over cloud entitlements. This webinar covers CIEM best practices, security framework standardization, entitlement cleanup with analytics, and how CIEM lays the foundation for posture management and DevSecOps.
July 23, 2025
Webinar


Automate the Identity Lifecycle with Microsoft Entra ID Governance
Automate the Identity Lifecycle with Microsoft Entra ID Governance
Microsoft Entra ID Governance's Lifecycle Workflows automate and streamline user identity lifecycle management to enhance security, improve compliance, and reduce administrative errors. This session covers customization, integration with external systems, and monitoring features to ensure efficient and secure identity governance.
July 23, 2025
Webinar


Achieving a Frictionless, Secure, and Passwordless User Authentication and Authorization Experience
Achieving a Frictionless, Secure, and Passwordless User Authentication and Authorization Experience
Explore strategies for delivering secure, passwordless authentication and authorization while keeping the user experience frictionless. This on-demand session shares practical approaches and IAM best practices for balancing usability with robust identity protection.
July 23, 2025
Webinar


All Access is Privileged – Taking a PAM-First Approach Towards your Identity Security Program
All Access is Privileged – Taking a PAM-First Approach Towards your Identity Security Program
Holistic identity security starts by treating all access as privileged and protecting sensitive data—no matter the role. A PAM-first approach defends against threats and enforces security for every user, not just IT admins.
July 23, 2025
Webinar


Configuring and Using Custom Claims in Microsoft Entra ID
Configuring and Using Custom Claims in Microsoft Entra ID
Microsoft Entra ID (formerly Azure AD) enables configuration of custom claims to enhance authentication and authorization workflows by providing additional data in tokens. This webinar covers how to set up and use custom claims in SAML, ID, and access tokens to deliver tailored application experiences and enforce fine-grained access controls.
July 23, 2025

Newsletter
Stay up to date with our monthly newsletter.
Covering the latest thought leadership, events, and news about identity security
What We Do
Capabilities
View All
Partners
© MajorKey 2025
Use of this site signifies your acceptance of MajorKey Tech's
Privacy Policy
.svg)

.svg)

































.svg)
