The Evolution of IAM: Transforming from Security Necessity to Strategic Value Driver
June 2, 2025
|
Duration:

In the last 20 years, Identity and Access Management (IAM) has evolved from a niche concept to a critical pillar of enterprise security and resilience. Driven by complex IT environments, tightening regulations, growing cyber threats and varying business drivers, organizations now prioritize advanced IAM solutions. However, rapid innovation has also introduced challenges—disjointed systems, rising costs, lack of relevant skills, and unclear ROI.
This article explores the evolution of IAM, common adoption hurdles, and the importance of empowering organizations to modernize their IAM strategies. It highlights how optimizing existing investments can help achieve measurable, sustainable value while consistently demonstrating business impact through ongoing progress.
The Origins of Identity and Access Management
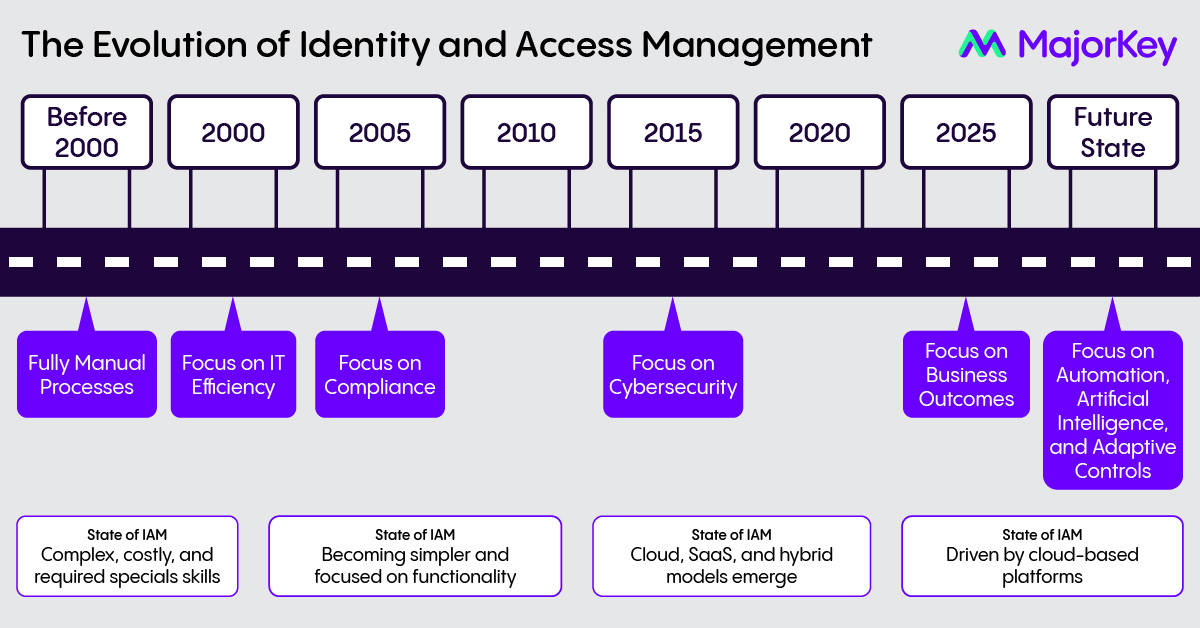
It is important to examine the evolution of IAM over the two plus decades. Technology vendors played a large role in shaping the market, defining features, setting standards and protocols, and creating foundational concepts and principles. When you examine the following diagram, one can notice some key things:
- Early IAM was dominated by complex, centralized solutions, but as organizations faced increasing costs and complexity, the market shifted toward simpler, modular, and more adaptable point solutions
- While the foundational principles didn’t change ,the impact of IAM gained much larger exposure and footprint
- It became clear that technology alone could not solve these challenges. People, process, and technology emerged as the three essential cornerstones for effective solutions
- Defining success had become myopic, highlighting the need for new ways to demonstrate ROI. Showing ongoing progress is now a key aspect of measuring value.
- Over the past two decades, the drivers for IAM programs have evolved from focusing primarily on IT efficiency to emphasizing business outcomes, driven by regulatory compliance and cybersecurity demands.
- Tools have become both a blessing and curse, due to factors such as high costs, complexity, overpromises by vendors, required skillsets, and overlapping feature
- While the impact is still unclear, Artificial Intelligence (AI) is emerging as a driver of innovation in the field
- The technology landscape remains complex, with a mix of niche players and converged solutions
The Current IAM Landscape - Driven by Business Outcomes
Since 2022, analysts such as Gartner have highlighted the importance of simplification and consolidation, resulting in mergers and acquisitions by major vendors and private equity firms. The use of cloud technologies has altered security paradigms, positioning identity as the new security perimeter. This shift, along with zero-trust security models, has enhanced the strategic importance of IAM. Chief Financial Officers are monitoring IAM investments more closely due to these trends:
- High-cost, complex projects: Multi-million-dollar initiatives with unclear ROI
- Extended deployments: Lengthy timelines with uncertain outcomes
- Value imperative: Increasing need to demonstrate measurable benefits across cybersecurity, IT, compliance, and business units
Most enterprises have invested in IAM, often across multiple technology platforms. However complexity, high costs, and unclear ROI, exacerbated by cloud identity demands and zero trust requirements, are undermining confidence in these programs.
AI is revolutionizing IAM by enhancing security, automating processes, and enabling adaptive controls. Gartner predicts that by 2026, over 60% of IAM platforms will incorporate AI, shifting IAM from static to adaptive and intelligent identity security.
Common Customer Pitfalls
Despite decades of investment, promises by technology vendors, and early AI advancements, organizations continue to face challenges such as:
- Technology Over-Reliance: Focusing solely on tools while neglecting process and governance frameworks
- Fragmented Investments: Multiple overlapping solutions inflate costs and complicate management
- Stakeholder Misalignment: Divergent priorities among IT, compliance, cybersecurity, and business teams hinder cohesive strategies
- Unclear ROI: Significant expenditures lack quantifiable outcomes, undermining executive support
- Flawed Definition of Success: Success was often defined by discrete streams of objectives which did not translate into meaningful, value-drive outcomes
- Lack of Awareness: Foundational concepts, appropriate drivers and relevant outcomes are often overlooked or misunderstood
In Conclusion
Whether it pertains to passwordless access, identity-first security, decentralized identity, or AI-powered IAM, the underlying issue remains consistent.
- Organizations need to adopt astrategy to balance efficiency, compliance, cybersecurity and business driven outcomes
- While the convergence of tools and platforms is the NorthStar, simplicity cannot be compromised
- IAM should be an enabler and ensure progress over time
- Relying on automation should be a key driver, but it’s important to be selective about what is automated
- While AI is promising, it’s important to adopt solutions that align with your overall strategy
- Spending should be tied to business outcomes and measurable progress.
Solving IAM Complexity: MajorKey's Blueprint for Success
MajorKey redefines IAM success by addressing these challenges holistically. We recognize that each customer’s IAM needs are unique and shaped by distinct business requirements, system integration demands, and compliance obligations. Whether a small enterprise or a global corporation, the complexity of IAM implementation remains a universal hurdle, one we are uniquely equipped to navigate. Our approach transcends traditional technology deployments, aligning cybersecurity, IT operations, compliance, and business goals to deliver measurable, enduring value. We achieve this through:
- Strategic Advisory Services: Comprehensive assessments to identify inefficiencies, eliminate redundancies, and develop tailored roadmaps that address each customer’s unique needs.
- Advanced Technology Integration: Streamlining multi-vendor environments, reducing platform sprawl, and maximizing the value of existing investments.
- Continuous Value Assurance: Real-time visibility into IAM outcomes, ensuring ongoing alignment with diverse customer priorities and evolving requirements.
- Continuous Progress Assurance: Defines and tracks measurable business-relevant metrics to demonstrate sustained progress.
MajorKey's Impact: Driving Strategic Value and Measurable Results in IAM
MajorKey transforms IAM into a strategic enabler, deliveringquantifiable benefits:
- Cost Efficiency: Reduces total cost of ownership by up to 30% through platform consolidation and optimized workflows
- Accelerated Delivery: Speeds deployments by up to 40% through proven methodologies and accelerators
- Enhanced Compliance and Security: Achieves regulatory and security objectives up to 25% faster
- Measurable Returns: Delivers a projected 3:1 ROI within 18 months, directly linking IAM investments to tangible business value.
Authors

No items found.
No items found.
No items found.
.svg)



















.svg)
